Codex CLI's Security Triple Play: Guardian Auto-Review, OTEL Hook Metrics, and MITM Pattern Matching
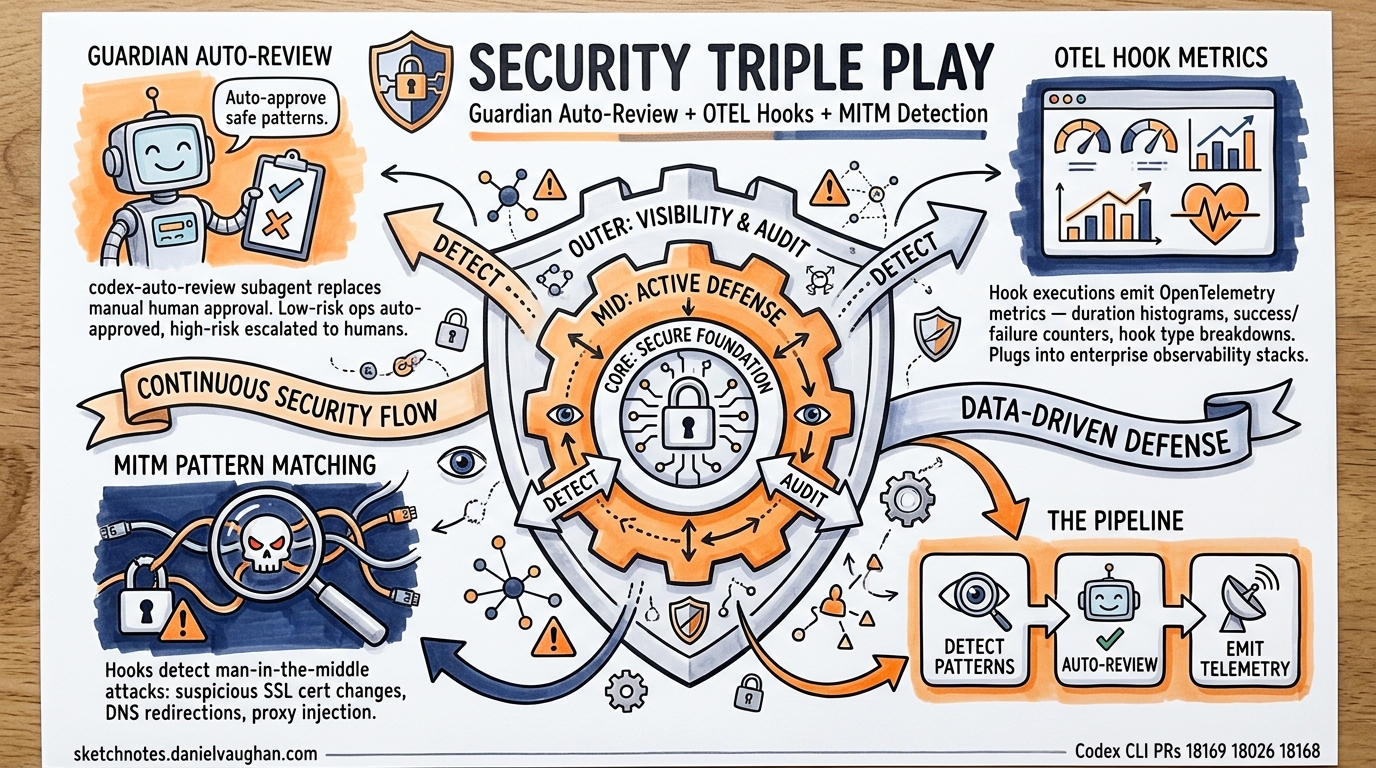
Three PRs merged on April 16, 2026 significantly strengthen Codex CLI’s enterprise security and observability story. Together, they form a coherent security pipeline: detect suspicious patterns → auto-review with guardian → emit telemetry for audit.
1. Guardian Auto-Review (PR #18169)
What changed: Guardian reviews now use codex-auto-review — an automated review subagent — instead of requiring manual human approval for every flagged operation.
Why it matters: In enterprise environments, the approval loop is the biggest source of friction. Developers running --auto-edit or suggest mode still hit walls when the guardian flags operations. Auto-review means the guardian can make informed pass/fail decisions on common patterns (e.g., safe file writes, known test commands) while still escalating genuinely risky operations to humans.
Agentic pod implications: This is a step toward fully autonomous agent pipelines. An orchestrator agent can now delegate tasks to specialist agents that run with guardian auto-review, reducing the human-in-the-loop bottleneck to only the highest-risk operations. Combined with the structured guardian output schema (PR #17061), you get machine-readable security decisions flowing through the pipeline.
2. OTEL Metrics for Hook Runs (PR #18026)
What changed: Hook executions now emit OpenTelemetry metrics — duration, success/failure counts, and hook type breakdowns.
Why it matters: Hooks are the primary extension point for enterprise governance (pre-commit checks, security scanning, compliance verification). Until now, there was no standardised way to monitor hook health at scale. OTEL metrics integrate directly with existing enterprise observability stacks (Datadog, Grafana, Splunk).
Key metrics likely emitted:
- Hook execution duration (histogram)
- Hook success/failure rate (counter)
- Hook type distribution (e.g., SessionStart, PreToolUse, PostToolUse)
Connects to: The article on Codex CLI OpenTelemetry observability now has a concrete new data source — hook-level telemetry.
3. Pattern Matching for MITM Hooks (PR #18168)
What changed: Hooks can now use pattern matching to detect man-in-the-middle (MITM) attack patterns — such as suspicious network redirects, certificate warnings, or unexpected proxy configurations.
Why it matters: As Codex agents gain more network access (MCP servers, API calls, package installations), the attack surface for MITM attacks grows. Pattern-matching hooks can detect:
- Unexpected SSL certificate changes during
npm installorpip install - Suspicious DNS redirections
- Proxy injection attempts within sandbox environments
Enterprise relevance: SOC2 and FedRAMP environments require evidence of network security monitoring. MITM detection hooks provide auditable evidence that agent network operations are monitored for tampering.
The Security Pipeline
These three PRs compose into a coherent enterprise security architecture:
Agent Operation
│
├─► MITM Pattern Hook (detect suspicious network activity)
│ │
│ └─► OTEL metrics (emit detection telemetry)
│
├─► Guardian Auto-Review (assess operation risk)
│ │
│ ├─► Auto-approve (low risk, known pattern)
│ └─► Escalate to human (high risk, unknown pattern)
│
└─► OTEL metrics (emit review decision telemetry)
Other Notable Merged PRs (April 16)
| PR | Title | Significance |
|---|---|---|
| #18070 | Extract plugin loading into codex-core-plugins | Modularisation for FedRAMP routing (see core plugins article) |
| #18089 | Wire remote MCP stdio through executor | Remote MCP execution closer to production |
| #18025 | Cover MCP stdio tests with executor placement | Test coverage for remote MCP |
| #17387 | Register agent tasks behind use_agent_identity | Identity system continues rollout |
| #18200 | Split codex op handlers | Internal architecture cleanup |
Open PRs to Watch
| PR | Title | Why It Matters |
|---|---|---|
| #18219 | Move Computer Use tool suggestion to core | Computer Use being promoted from experimental to core |
| #18213 | Skill metadata budget handling | Token budget management per skill — cost governance |
| #18225/18226 | Turn environment list API | New API surface for environment-aware agent turns |
| #18222 | /plugins v2 tabbed marketplace menu | New plugin browsing experience |
| #18215 | Unify approval request routing | Architectural consolidation of approval flows |